What do you guys use to expose private IP addresses to the web? I was using the npm proxy manager with Cloudflare CDN. However, it stopped working after I changed my router (I keep getting error 521). Looking for an alternative to Cloudflare cdn so I can access my media server/self-hosted services away from LAN.
(Tailscale doesn’t work for me at all)
This is what I want to achieve: https://youtu.be/c6Y6M8CdcQ0?feature=shared
I literally followed this tutorial to make it work the first time.
Zerotier, although it’s similar to tailscale so you might have issues with it too
Thank you, will check it out.
521 usually means they cannot reach your server properly. Was the router change due to a new ISP, and does the new ISP block port 80/443? Did you re-make all the relevant port forwarding rules? Changing CDN won’t change anything if your ports are closed/not responding as expected.
Changing to a new internet plan, so they had to replace the router. Also, I did reopen ports 80 and 443, and I tested them. They’re working. What I noticed was Cloudflare changing the
A IP address to proxied (before it was the private server IP address, I got error 522 back then. I followed the tutorial again but got 521 error).
521 = Origin server down; I.e. the port is not open and/or the IP address is incorrect all together.
522 = Origin server time out; I.e. the port might be open but no content is being sent back.
If you’re seeing 521, then Cloudflare cannot establish a connection to port 80/443 on your IP address in the A record. Bearing in mind that in order for someone from outside of your LAN (i.e CloudFlare) to have access to your services, they must be able to reach the service, so this value should be your external IP address, not an internal address. Once you have your external address keyed into the record, have someone else not in your home try to access that IP/port combination and see what happens. If they cannot access, then port forwarding is not setup or your ISP is blocking, or you’re behind some CGNAT. If they can access, then something else is at play (origin IP filtering comes to mind).
This might help, sorry if it doesn’t, but here is a link to CloudFlares 5xx error code page on error 521. If you’ve done everything in the resolution list your ISP might be actively blocking you from hosting websites, as it is generally against the ISPs ToS to do such on residential service lines. This is why I personally rent a VPS and have a wireguard VPN setup to host from the VPN, which is basically just a roll your own version of Tailscale using any VPS provider. This way you don’t need to expose anything via your ISPs router/WAN and they can’t see what you are sending or which ports you are sending on (other than the encrypted VPN traffic to your VPS of course).
If you need public access:
https://github.com/anderspitman/awesome-tunneling
From this list, I use rathole. One rathole container runs on my vps, and another runs on my home server, and it exposes my reverse proxy (caddy), to the public.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters CGNAT Carrier-Grade NAT IP Internet Protocol NAT Network Address Translation VPN Virtual Private Network VPS Virtual Private Server (opposed to shared hosting)
[Thread #588 for this sub, first seen 11th Mar 2024, 01:45] [FAQ] [Full list] [Contact] [Source code]
tunnelbroker.net since I don’t have static IPv6 currently. Otherwise, that.
Can I ask why tailscale doesn’t work?
I have a headscale instance running in oracle’s free tier and can get to everything else through that.
Are you testing that the ports are open with your phone on a cellular network and not WiFi within the same network? Your router may be doing a loop back NAT which “forwards” the ports internally but isn’t necessarily forwarding the ports externally.
Did you change ISPs at all? I think I read that the router was new—is it a router/modem combo? If the ISP has changed it’s possible the new one doesn’t allow traffic on those ports, which is the case for my ISP. No amount of forwarding rules will change that.
If you have a separate modem/gateway and router it’s possible there are firewall rules on the device closer to the WAN in which case you may need to ask your ISP if they can put the modem in “pass through mode” in order to allow the traffic. That’s probably not the technical term for it—I think behind the scenes they either just disable the firewall or put the router address into DMZ, but that description has worked with me in the past with L1 support for them to know what I’m trying to accomplish.
Thanks everyone for your help.
I have fixed it by not using the npm proxy manager and only Cloudflare tunnels.
This video helped me
The only issue this method has is the upload limit of 100mb
I’m using services such as:
- Immich
- Nextcloud
- Jellyfin
- Valutwarden
New Lemmy Post: Cloudflare Alternative (https://lemmy.world/post/12975734)
Tagging: #SelfHosted(Replying in the OP of this thread (NOT THIS BOT!) will appear as a comment in the lemmy discussion.)
I am a FOSS bot. Check my README: https://github.com/db0/lemmy-tagginator/blob/main/README.md
Wireguard.
Unless you actually have a need for the public to access the services then you shouldn’t be exposing them. If it’s just you and a few household members that need access then you should be using ddns and wireguard, or similar.
My phone auto connects with wireguard as soon as I leave my home ssid, so I never lose access to my services.
My phone auto connects with wireguard as soon as I leave my home ssid, so I never lose access to my services.
How do you do that? Tasker?
I’m on iOS and do the same thing.
The WireGuard app has a setting to “connect on demand”. It’s in the individual connections/configurations.
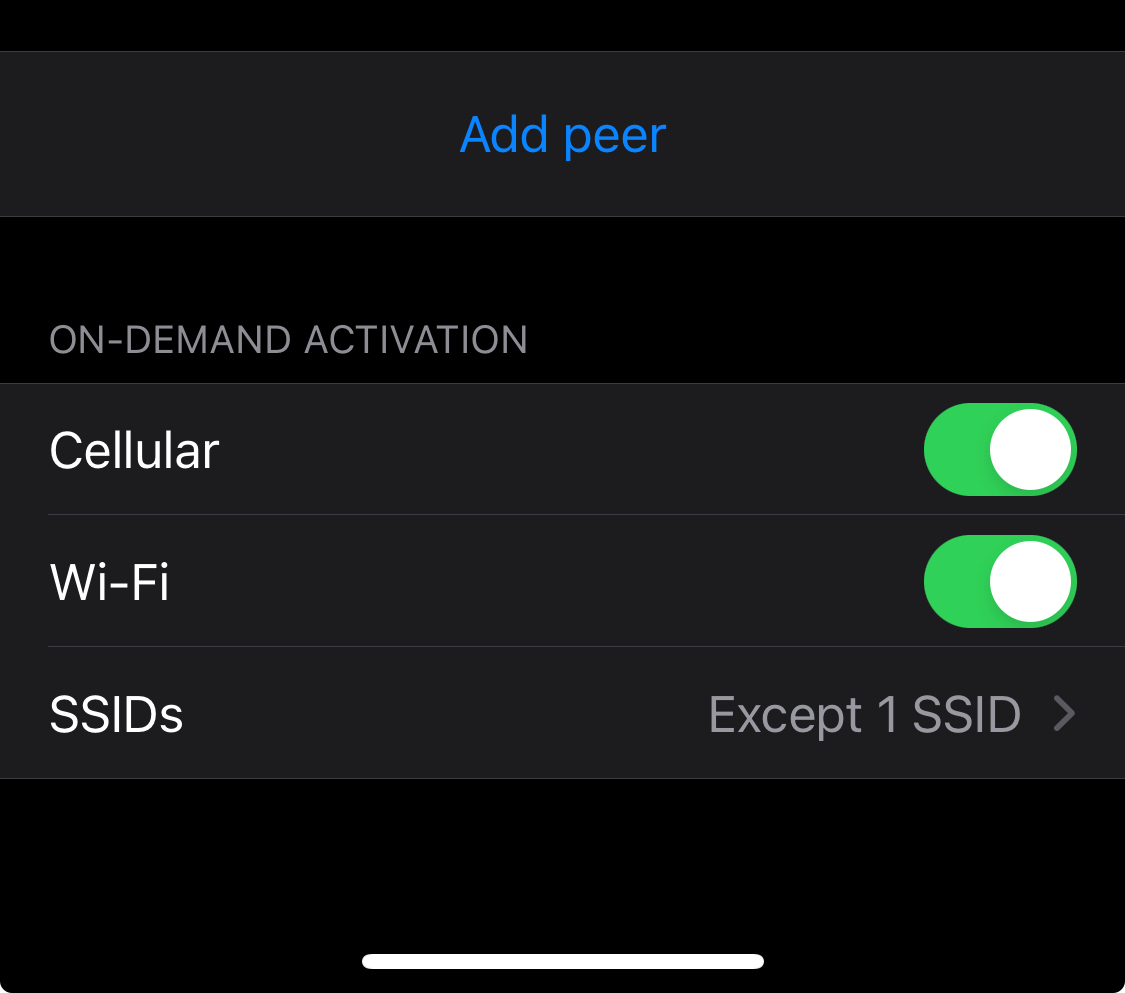
You can then set either included or excluded SSIDs. There’s also an option to always connect when you’re on mobile/cellular data.
I imagine the Android app is similar.
Not OP but I’ve been playing with Wireguard (and failing) for a short while and have noticed an option in my Android Phone’s settings to always connect to this VPN. Probably that






